This neat trick allows you to see the source and destination IP county. At least the country listed in the MaxMind databases. Keep in mind you could have a US IP address say from PureVPN connecting to you, and the user is actually in the country of Bolivia.
There are literally hundreds of thousands of IPs that are owned by VPN companies who will lease out VPN connections so anyone who pays including perps. The actors or perps can now pick and choose where they want to pretend to be from anywhere in the world. Most good hackers will use multiple VPN’s and multiple countries(you know on tv when McGeek say “Its gonna take a while gibs, they are bouncing off routers all over the place”. So you have to go pretty far down the rabbit hole to find the actual source. But this does give you insight into honest folks, and kiddie hackers.
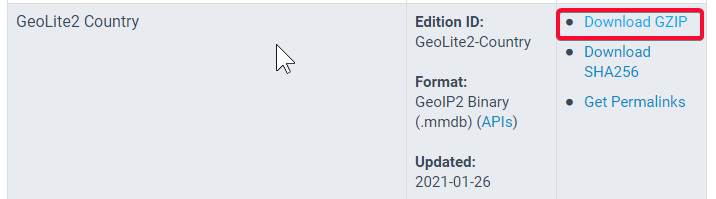
Get the Database
- Create a account at https://www.maxmind.com/ for the GeoLit2
- Download the GZip for GeoLit2 Country
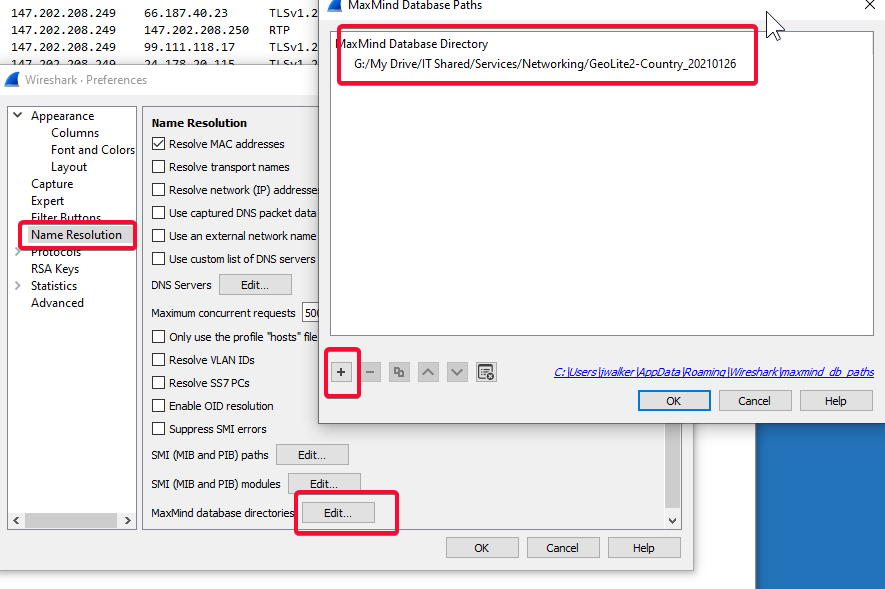
- I save my database folder on Google Drive File stream (you can use drive also, but I recommend don’t use the free drive), and mark it as offline. that way if any of my coworkers need to use it also, then can do the same.
Setup Wireshark
- Go to Wireshark >> Edit >> Preference >> Name Resolution and add the MaxMind database folder
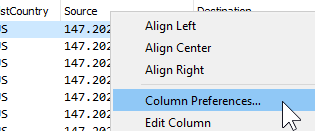
- Now right click the Column header and select Column Preferences
- Add both columns for the ip.geoip.src_country_iso and ip.geoip.dst_country_iso and drag to the column order you want
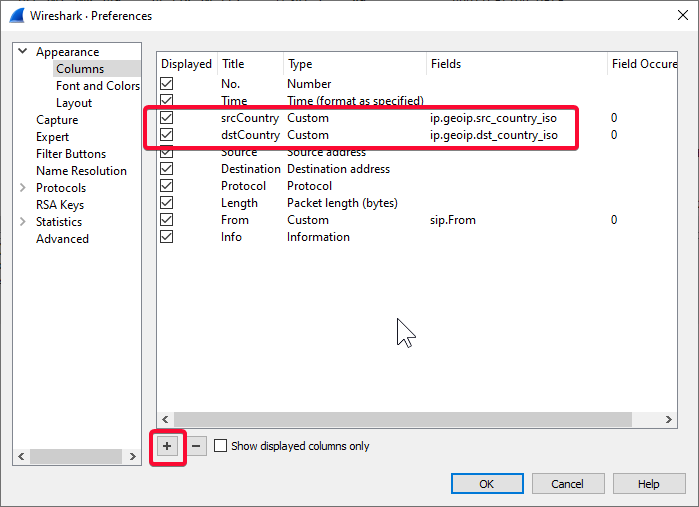
- Finally you need to restart WireShark for this to take affect. NOTE you can see the countries for public static IP addresses in both live captures and files you newly open up.
Enjoy!

